It takes exactly one compromised email account to jeopardize a multi-million Riyal contract. Saudi Aramco knows this, which is why the Third-Party Cybersecurity Standard (TPCS, February 2026) update places a relentless spotlight on how vendors secure their communications.
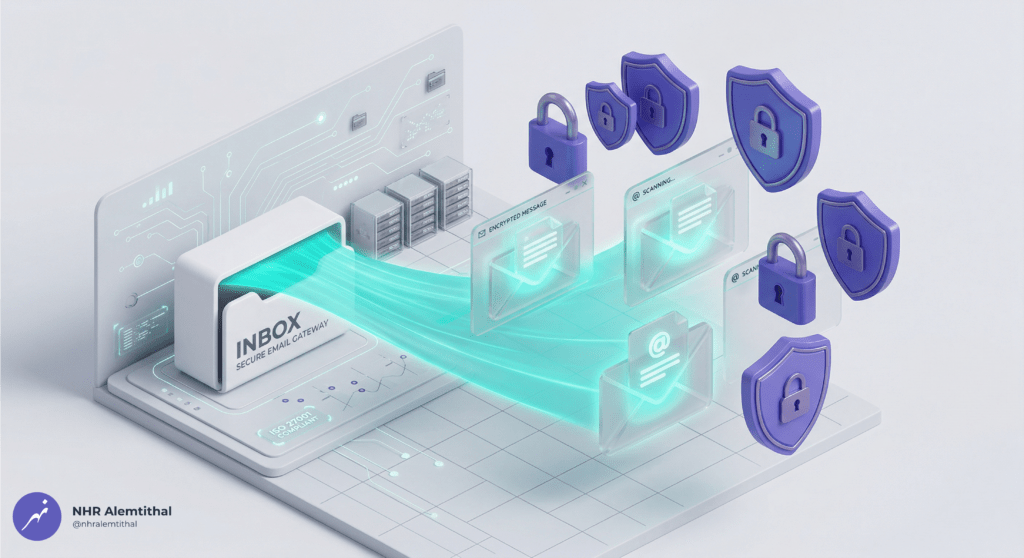
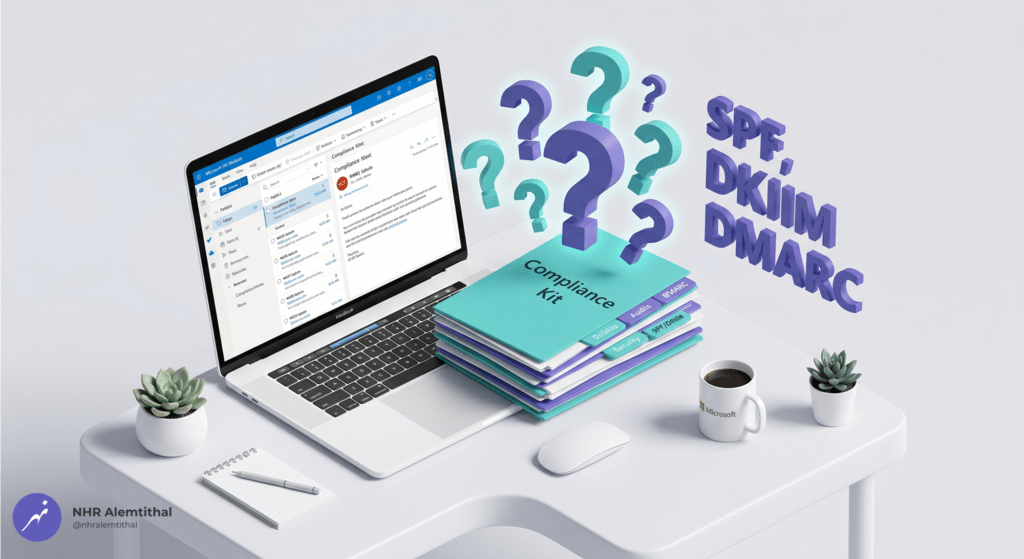
For SMEs in Dammam and Jubail, basic spam filters are no longer sufficient to pass the CCC audit. Auditors now strictly mandate the implementation of complex authentication protocols (SPF, DKIM, and DMARC), alongside advanced attachment scanning and the automatic blocking of external macros.
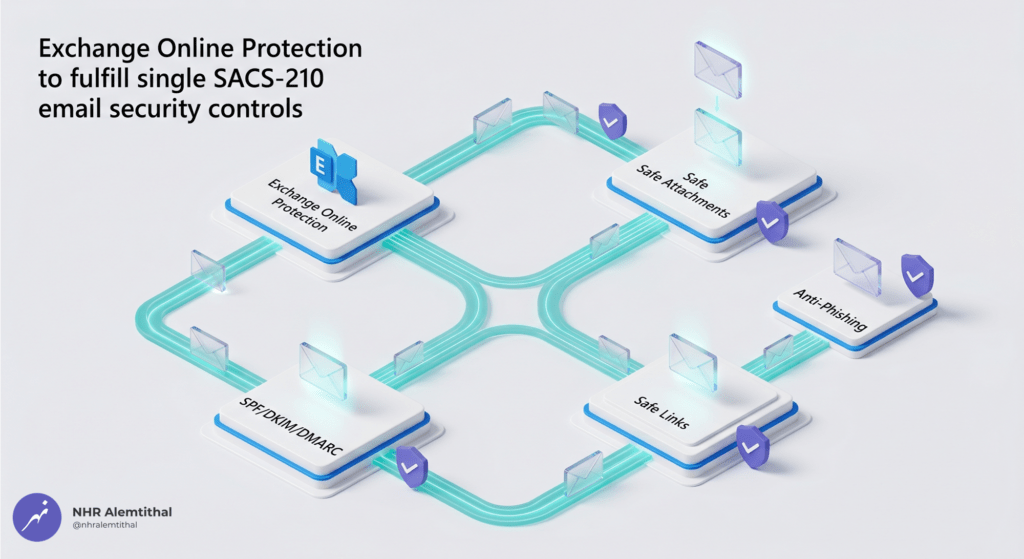
Fortunately, Microsoft Exchange Online combined with Microsoft Defender for Office 365 provides the enterprise-grade email security necessary to check these boxes. This guide reveals how to configure these tools to lock down your communications and breeze through the email security portion of your CCC audit.
Why Exchange Online and Defender for Office 365 Are Essential for TPCS Compliance
Email remains the primary attack vector for cybercriminals targeting Saudi businesses. The TPCS recognizes this threat landscape and mandates comprehensive email security controls that go far beyond basic spam filtering. Microsoft Exchange Online and Defender for Office 365 work together to provide layered protection that satisfies these requirements while maintaining business productivity.
Key Advantages for TPCS Compliance
- Email Authentication Enforcement: Built-in support for Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain Message Authentication Reporting (DMARC) perfectly satisfies
TPC1.20requirements. - Advanced Threat Protection: Safe Attachments technology uses machine learning and sandboxing to detect zero-day malware, satisfying
TPC1.22requirements for inspecting email attachments with signature analysis. - Anti-Phishing and Anti-Spam: Exchange Online Protection (EOP) provides enterprise-grade spam filtering that meets
TPC1.21requirements to inspect all incoming emails originating from the Internet. - Macro Blocking: Automatic blocking of Office macros from external sources directly addresses
TPC1.24requirements, preventing macro-based malware infections. - Private Domain Enforcement: Exchange Online allows you to enforce the use of a private email domain, ensuring compliance with
TPC1.23prohibitions against using generic public domains like Gmail or Hotmail for business communications. - Comprehensive Audit Logging: Unified audit logs capture email security events, supporting
TPC1.31requirements for activating cybersecurity event logs.
Critically, these Microsoft tools are licensed per user, scale seamlessly from small teams to enterprise deployments, and receive continuous threat intelligence updates—reducing the operational burden on your SME’s IT team.
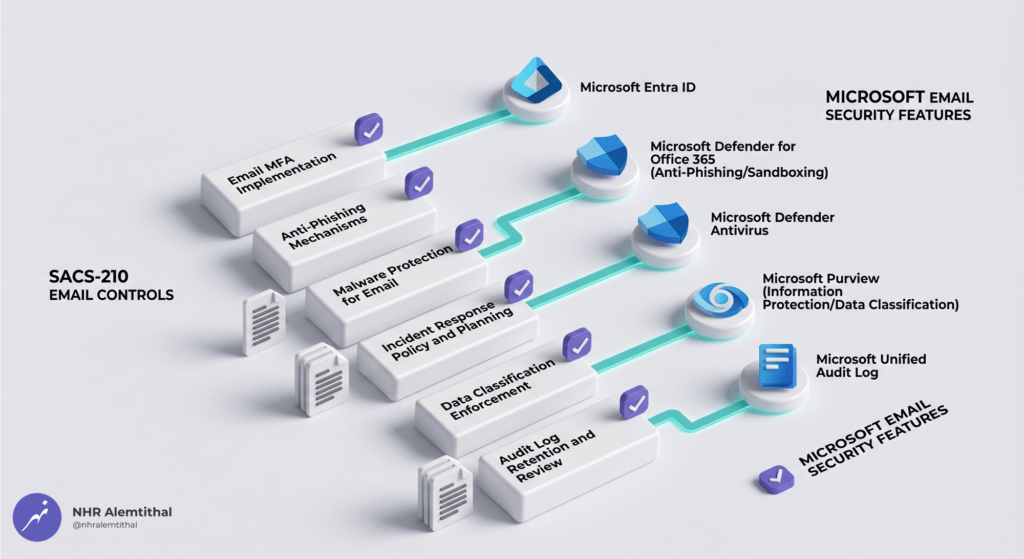
TPCS Control Mapping: How M365 Email Security Addresses Key Requirements
The table below maps specific TPCS General Requirements controls (TPC1.20 through TPC1.32) to Exchange Online and Microsoft Defender for Office 365 capabilities. This reference helps you prioritize configuration tasks during your compliance rollout.
| TPCS Control | Requirement Summary | Exchange Online / Defender Feature | Configuration Guidance |
|---|---|---|---|
TPC1.20 | Implement SPF, DMARC, DKIM on mail server | SPF, DKIM, DMARC configuration | Publish your SPF record; enable DKIM signing in the portal; configure DMARC policy in DNS. |
TPC1.21 | Inspect incoming emails using anti-spam | EOP anti-spam & anti-phishing | Configure anti-spam policies; enable spam quarantine; configure safe/blocked sender lists. |
TPC1.22 | Inspect email attachments with signature analysis | Safe Attachments sandbox analysis | Enable Safe Attachments for all emails; configure explicit blocking actions for threats. |
TPC1.23 | Use private email domain (no Gmail/Hotmail) | Custom domain enforcement | Add and verify your company domain; set as primary; block outbound use of generic domains. |
TPC1.24 | Auto-block Office Macros from external sources | Safe Attachments macro restrictions | Configure macro blocking for external files in EOP; enable Safe Documents. |
TPC1.31 | Activate audit and cybersecurity event logs | Unified Audit Log for email events | Enable audit logging in Purview; configure retention; monitor the Threat Explorer. |
TPC1.32 | Notify proponent within 24 hours of incident | Automated incident response | Configure alert policies; establish internal incident response procedures to meet the 24-hour SLA. |
Note: Exchange Online and Defender for Office 365 directly address the heavy technical requirements for email security. However, technical software cannot write your corporate policies. The remaining controls require formal administrative documentation— which is where the TPCS Compliance Kit is vital.
The Documentation Gap: Why Technology Alone Is Not Enough
While Microsoft’s email security tools provide powerful protections, Saudi Aramco authorized auditors require documented evidence that governance policies exist, procedures are followed, and compliance is actively managed. This is the “documentation gap” that causes many SMEs to fail their initial CCC audit.
For example:
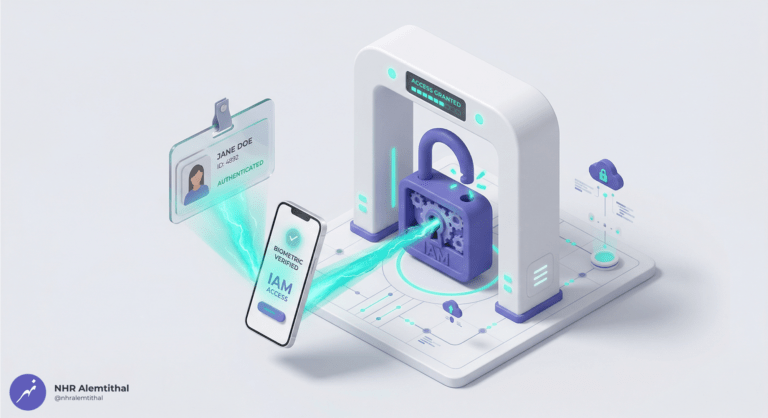
TPC1.2requires an approved Acceptable Use Policy (AUP) defining email rules—Exchange Online does not generate this legal document for you.TPC1.4mandates formal employee onboarding procedures including email account provisioning—you must maintain the actual operational checklists.TPC1.14demands an annual access review report for email accounts—audit logs must be extracted, analyzed, and formally documented into a presentation.
This is precisely why we developed the TPCS Compliance Kit. It provides the premium policy templates, operational forms, dynamic registers, and reporting frameworks that map directly to each TPCS control.
Integrating M365 Email Security with the TPCS Compliance Kit
| Compliance Requirement | Exchange Online & Defender Deliver | TPCS Compliance Kit Delivers |
|---|---|---|
| Policy Documentation | Technical enforcement tools. | Professionally drafted email security policies mapped to TPCS. |
| Evidence Collection | Message trace reports and raw audit logs. | Pre-formatted presentation reports designed for auditor submission. |
| Process Workflows | Automated email flow rules. | Formal Email Provisioning/Deprovisioning Checklists. |
| Audit Submission | Technical dashboards. | Final Technical Report summarizing your email security posture. |
When utilized together, Exchange Online handles the technical email protection, while the TPCS Compliance Kit provides the exact administrative evidence authorized auditors expect to see.
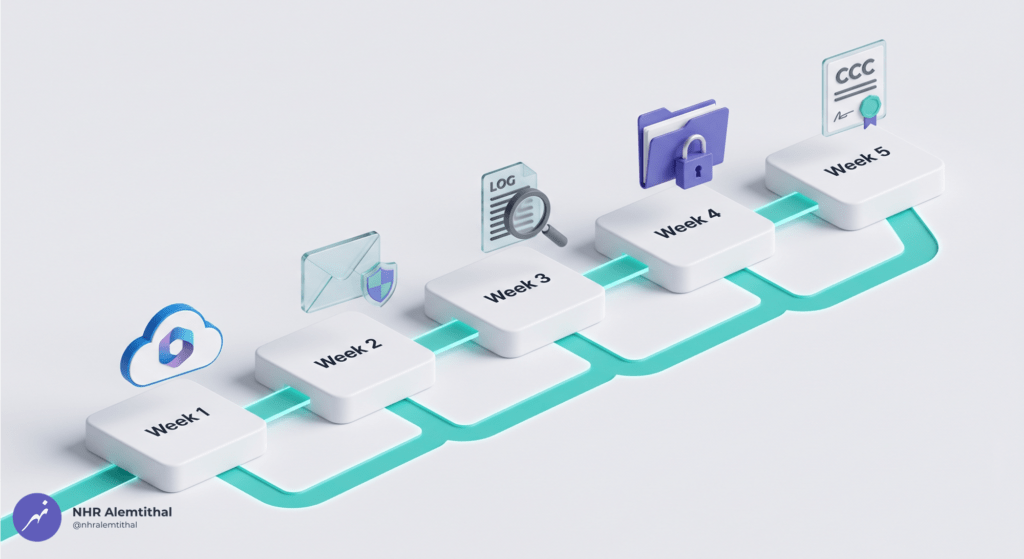
Step-by-Step Implementation Guide
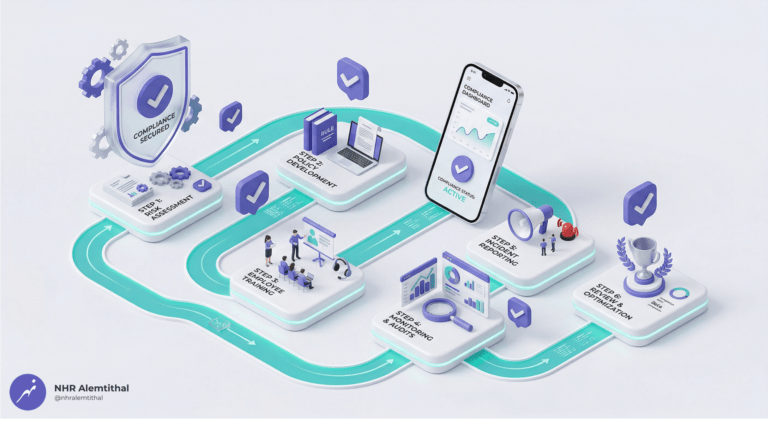
Follow this structured, 5-week approach to configure your Microsoft email security environment for TPCS compliance while integrating your documentation toolkit.
Phase 1: Foundation Setup (Week 1)
- Procure Licenses: Obtain Microsoft 365 Business Premium (which includes Exchange Online and Defender) directly through our Contact Us.
- Add and Verify Your Private Domain: Access the Microsoft 365 Admin Center to add your company domain and verify ownership to satisfy
TPC1.23. - Configure Base DNS Records: Publish your initial SPF record (
v=spf1 include:spf.protection.outlook.com -all). - Create User Mailboxes: Assign licenses to all users and enforce password resets on their first login.
Phase 2: Email Security Configuration (Week 2)
- Enable DKIM Signing: In the Microsoft 365 Defender Portal, navigate to Threat Policies, select your domain, enable DKIM signing, and publish the required CNAME records.
- Configure DMARC Policy: Create and publish your DMARC TXT record (start with
p=quarantineorp=nonefor monitoring). - Configure Exchange Online Protection (EOP): Set up aggressive inbound anti-spam filtering, enable spam quarantine, and configure anti-phishing with impersonation detection.
- Enable Defender for Office 365 Features: Configure the Safe Attachments policy for all emails (internal and external) and set up Safe Links for URL scanning.
- Configure Macro Blocking: In your anti-malware policies, explicitly enable the blocking of Office macros originating from external sources to satisfy
TPC1.24.
Phase 3: Monitoring and Audit Configuration (Weeks 2-3)
- Enable Unified Audit Logging: Access the Purview Compliance Portal and enable audit log retention (minimum 1 year for TPCS).
- Configure Alert Policies: Create alerts for malware detection, phishing attempts, and mass email forwarding to ensure you can meet the 24-hour incident notification rule (
TPC1.32). - Test Controls: Send test emails to verify Safe Attachments and validate your SPF/DKIM/DMARC records using external tools like MXToolbox.
Phase 4: Documentation Integration (Week 3)
- Download the TPCS Compliance Kit (Feb 2026 Standard).
- Customize Email Security Policies: Update the Acceptable Use Policy and Cybersecurity Policy with your company details using “Find and Replace.”
- Complete Operational Forms: Integrate the Email Account Provisioning/Deprovisioning checklists into your HR workflows.
- Generate Audit Evidence: Export screenshots of your DKIM status, DMARC DNS records, Safe Attachments configurations, and anti-spam settings.
- Compile the Kit: Paste your screenshots into the pre-formatted Email Security Configuration Report templates.
Phase 5: Audit Preparation and Submission (Week 4)
- Conduct an Internal Pre-Audit Review: Use the Compliance Kit’s Email Security Checklist.
- Engage an Authorized Audit Firm: Select an auditor from Saudi Aramco’s approved list.
- Submit Your Compliance Report: Hand over your perfect blend of technical email evidence and Kit-generated policy documentation.
- Receive Your CCC Certificate: Submit it to the Saudi Aramco e-Marketplace.
Common Email Security Implementation Mistakes and How to Avoid Them
Even with Exchange Online and Defender properly licensed, SMEs frequently misconfigure the environment. Avoid these common audit pitfalls:
- Publishing SPF Without Testing: Publishing a hard-fail SPF record without verifying all legitimate email sources can cause severe delivery failures. Solution: Start with SPF in monitoring mode (
~all), use message trace to identify all sources, then switch to hard fail (-all). - Enabling DKIM Without DNS Verification: Enabling DKIM in M365 without properly publishing the CNAME records in your DNS causes authentication failures. Solution: Use DNS propagation checkers before enabling the feature in the portal.
- Setting DMARC to Reject Too Early: Setting
p=rejectimmediately will block legitimate emails. Solution: Start withp=nonefor 30 days to analyze reports, move top=quarantine, and finally implementp=reject. - Safe Attachments Not Applied Globally: Creating the policy but failing to apply it to all internal and external emails leaves gaps (violating
TPC1.22). Solution: Ensure the policy scope includes “All recipients.” - Audit Logging Not Enabled: The unified audit log is not always enabled by default, violating
TPC1.31. Solution: Explicitly enable audit logging in the Purview Compliance Portal and set retention to at least 365 days. - Macro Blocking Ignored: Relying solely on antivirus rather than explicitly configuring macro blocking for external files violates
TPC1.24. Solution: Enable the Safe Documents feature and configure explicit macro blocking in your anti-malware policy.
Frequently Asked Questions
Q1: Can Exchange Online and Defender for Office 365 alone achieve TPCS compliance?
A: No. While they flawlessly handle the technical requirements for email authentication, anti-spam, attachment scanning, and macro blocking, the remaining controls require documented policies and procedures. The TPCS Compliance Kit provides the missing administrative framework.
Q2: Do I need both Exchange Online and Defender for Office 365?
A: Yes. Exchange Online provides the foundation (private domain, SPF, basic anti-spam), but Defender for Office 365 is strictly essential for the advanced threat protection (Safe Attachments, Safe Links) required to satisfy TPC1.21 and TPC1.22.
Q3: How do I procure these Microsoft licenses?
A: As an authorized Microsoft Cloud Solution Provider (CSP) based in Dammam, NHR Alemtithal offers direct procurement through our secure store. Both are included seamlessly within Microsoft 365 Business Premium. Contact Us for your Microsoft 365 Subscriptions.
Q4: Can the TPCS Compliance Kit be used with other email platforms?
A: Yes. The administrative policies and registers in the Compliance Kit are platform-agnostic. However, the Technical Implementation guide is highly optimized for Microsoft 365 environments.
Q5: How long does DMARC take to fully implement?
A: A safe DMARC implementation follows a phased approach: monitoring (p=none) for a few weeks to analyze reports, moving to p=quarantine, and finally p=reject. For TPCS audit purposes, you can demonstrate compliance with DMARC configured in quarantine mode, though reject is best practice.
Q6: What if we already have a third-party email security solution?
A: If you use Proofpoint or Mimecast, you may not need Defender features. However, for TPCS compliance, you must still provide evidence of SPF/DKIM/DMARC, attachment scanning, and external macro blocking. If your existing solution provides these, simply document it using our kit.
Q7: Does this approach support NCA ECC 2:2024 and Saudi PDPL compliance?
A: Yes. The TPCS Compliance Kit is explicitly mapped to the NCA ECC 2:2024 and Saudi PDPL frameworks. Exchange Online’s robust encryption, authentication, and auditing capabilities align perfectly with these national standards.
Q8: What if we lack internal IT expertise to configure Exchange Online?
A: The TPCS Compliance Kit includes a plain-English Technical Implementation Checklist designed to be handed off to any qualified IT consultant or Managed Service Provider (MSP) to configure your DNS records and anti-phishing policies.
Q9: Can we use Exchange Online with our existing custom domain?
A: Yes. You will verify domain ownership via a DNS TXT record, update your MX records to route email to Exchange Online, and publish your new SPF, DKIM, and DMARC records.
Q10: What ongoing maintenance is required after certification?
A: Cybersecurity Compliance Certificate is valid for two years. You must maintain your Microsoft subscriptions, monitor DMARC reports weekly, review Safe Attachments detection reports, conduct annual access reviews for email accounts, complete yearly staff cybersecurity training, and prepare for a simplified re-audit.

Accelerate Your Email Security Compliance Journey
Achieving Third-Party Cybersecurity Standard (TPCS) email security compliance does not require enterprise budgets or a massive cybersecurity department. With Exchange Online and Defender for Office 365 acting as your technical foundation, and the TPCS Compliance Kit serving as your administrative framework, Saudi SMEs can secure their Aramco CCC certification efficiently and affordably.
Your Next Steps
- Procure Licenses: Set up your technical foundation by purchasing Microsoft 365 Business Premium (which includes Exchange Online and Defender).
- Download the TPCS Compliance Kit: Access all 17 auditor-ready templates.
- Configure DNS Records: Implement SPF, DKIM, and DMARC using the included technical checklist.
- Customize Your Evidence: Prepare your audit package using the customized Word and Excel documents.
- Engage an Auditor: Submit your perfectly aligned documentation and secure your contract.
Do not let fragmented email configurations and missing paperwork delay your Aramco partnership.
Disclaimer: Microsoft Exchange Online and Defender for Office 365 provide technical capabilities that support TPCS compliance. Proper configuration, ongoing management, and documented evidence are required to achieve certification. The TPCS Compliance Kit provides templates to support your efforts; template usage alone does not constitute certification. Organizations remain solely responsible for their cybersecurity posture and for validating compliance through an authorized third-party audit.