Identity is the new security perimeter. If you are preparing for a Saudi Aramco CCC audit under the new SACS-210 guidelines, authorized auditors won’t just ask about your firewalls—they will forensically examine how your employees log in to your systems.
Weak passwords, shared generic accounts, and unprotected remote access are now immediate disqualifiers. The February 2026 update demands granular, strictly enforced access controls across your entire organization.
You do not need to build a complex identity infrastructure from scratch. Microsoft Entra ID Plan 1 provides a comprehensive, cloud-based identity platform that flawlessly executes Multi-Factor Authentication (MFA) and Conditional Access exactly where SACS-210 requires it. Here is how to configure it for your next audit.
Why Microsoft Entra ID Plan 1 Is Essential for SACS-210 Compliance
Identity is the new security perimeter. SACS-210 recognizes this reality by dedicating a massive portion of its PROTECT domain specifically to identity management, authentication, and access control. Microsoft Entra ID Plan 1 delivers exactly what auditors are looking for at a predictable, per-user subscription cost.
Key Advantages for SACS-210 Compliance
- Centralized Authorization: Entra ID provides the centralized corporate identity and access management solution explicitly demanded by the standard.
- Granular Password Policies: Enforce the exact 8-64 character limits, including uppercase, lowercase, digits, and special characters, while actively preventing password hints.
- Conditional Access & MFA: Blanket MFA is often disruptive. Entra ID Plan 1 allows you to deploy Conditional Access policies that surgically enforce Multi-Factor Authentication (MFA) precisely where SACS-210 requires it: remote access, cloud services, and privileged accounts.
- Single Sign-On (SSO): Securely integrate your third-party applications with SSO, enforcing MFA upon initial login to satisfy strict session controls.
- Automated Offboarding: Instantly revoke access to all corporate resources when an employee leaves, supporting mandatory offboarding and notification requirements.
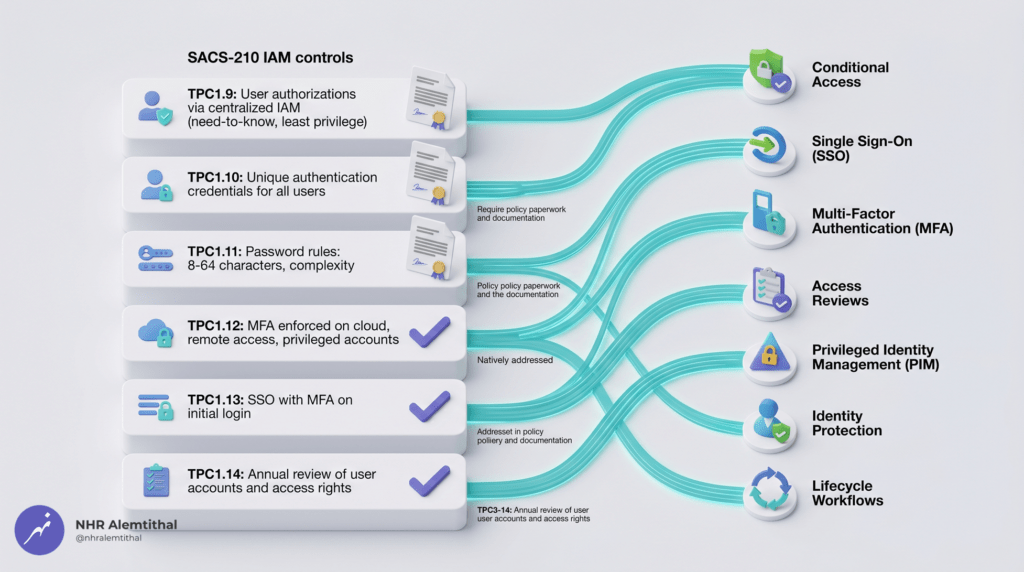
SACS-210 Control Mapping: How Entra ID Addresses Key Requirements
The table below maps specific SACS-210 General Requirements controls (TPC1.1 through TPC1.33) to Microsoft Entra ID Plan 1 capabilities. This reference helps prioritize configuration tasks during your compliance rollout.
| SACS-210 Control | Requirement Summary | Microsoft Entra ID Feature | Configuration Guidance |
| TPC1.9 | Centralized IAM, Least Privilege, Need-to-Know | Entra ID Directory & RBAC | Establish Entra ID as your centralized directory; assign strict Role-Based Access Control (RBAC). |
| TPC1.10 | Unique authentication credentials | User Accounts | Ensure every employee has a unique identity; strictly prohibit generic or shared accounts. |
| TPC1.11 | Strict password rules (8-64 chars, complex, no hints) | Custom Password Protection | Configure password policies in Entra ID to enforce exact length and complexity requirements. |
| TPC1.12 | MFA enforced on remote, cloud, and privileged access | Conditional Access Policies | Create robust Conditional Access rules to trigger MFA based on location, app, and user role. |
| TPC1.13 | SSO must use MFA on initial login | Single Sign-On (SSO) | Integrate SaaS apps via Enterprise Applications; ensure Conditional Access applies to the SSO gateway. |
| TPC1.14 | Annual review of user accounts and access rights | Access Reviews (Note: Requires P2 or manual export) | Export user and role reports from Entra ID to conduct and document your annual access reviews. |
| TPC1.33 | Notify proponent when access is no longer needed | Sign-in Logs & Account Disabling | Disable accounts immediately upon offboarding; use logs to verify no further access attempts occurred. |
Note: Microsoft Entra ID Plan 1 directly addresses the technical execution of SACS-210 identity controls. However, a flawlessly configured cloud directory cannot write your corporate policies. The remaining controls require formal administrative documentation—which is where the SACS-210 Compliance Kit is essential.
The Documentation Gap: Why Technology Alone Is Not Enough
While Microsoft Entra ID provides powerful technical safeguards, Saudi Aramco authorized auditors require documented evidence that governance policies exist, procedures are systematically followed, and compliance is actively managed. This is the “documentation gap” that causes many SMEs to fail their initial CCC audit.
For example:
- TPC1.4 mandates a formal documented process for onboarding and offboarding employees (including background checks and access removal). Entra ID handles the technical removal, but you must maintain the actual operational checklists.
- TPC1.14 demands an annual review of user accounts. You must extract data from Entra ID, format it, and present a formal Access Review Report to the auditor.
- TPC1.2 requires an approved Acceptable Use Policy (AUP) defining how employees handle their credentials. Microsoft does not generate this legal document for you.
This is precisely why we developed the SACS-210 Compliance Kit. It provides premium policy templates, operational forms, dynamic registers, and reporting frameworks that map directly to each SACS-210 control.
Integrating Entra ID Plan 1 with the SACS-210 Compliance Kit
| Compliance Requirement | Microsoft Entra ID Delivers | SACS-210 Compliance Kit Delivers |
| Policy Documentation | Technical enforcement via Conditional Access. | Professionally drafted Access Management policies mapped to SACS-210 and NCA ECC 2:2024. |
| Process Workflows | Fast account provisioning and disabling. | Formal Employee Onboarding/Offboarding Checklists and AUP Acknowledgment Forms. |
| Evidence Collection | Sign-in logs and user directory exports. | Pre-formatted Access Review Reports and presentation formats designed for auditor submission. |
| Audit Submission | Technical dashboards. | Final Technical Report summarizing your IAM security posture. |
When utilized together, Entra ID handles the heavy technical identity protection, while the SACS-210 Compliance Kit provides the exact administrative evidence authorized auditors expect to see.

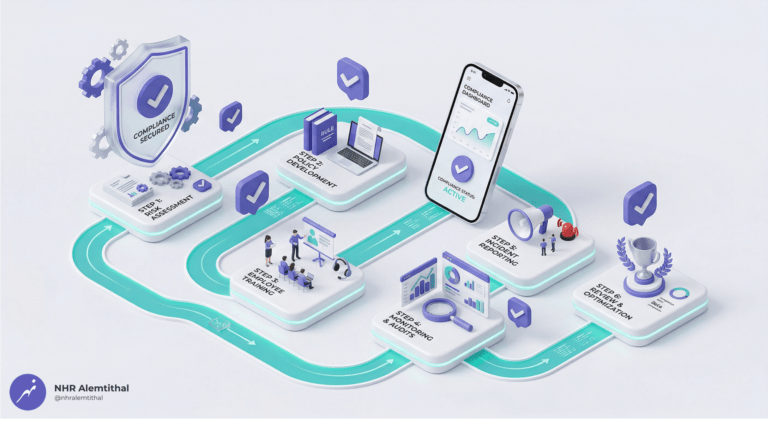
Step-by-Step Implementation Guide
Follow this structured, 4-week approach to configure Microsoft Entra ID Plan 1 for SACS-210 compliance while integrating your documentation toolkit.
Phase 1: Foundation Setup (Week 1)
- Procure Licenses: Obtain Microsoft Entra ID Plan 1 (available standalone or natively included in Microsoft 365 Business Premium) directly through our NHR Alemtithal Store.
- Configure the Tenant: Set up your custom domain and ensure all users have unique identities assigned. Disable any legacy shared accounts (e.g., info@, sales@) that are used for interactive logins.
- Enforce Password Policies: Configure Entra ID Password Protection to enforce the 8-64 character limit, complexity requirements, and block common weak passwords.
Phase 2: Security Policy Configuration (Week 2)
- Configure Conditional Access: This is the most critical step. Build policies that explicitly require MFA for:
- All remote access (including access from the internet).
- Access to all cloud services.
- Any user with privileged admin roles.
- Configure Single Sign-On (SSO): Connect your third-party SaaS applications (like HR systems or CRM) to Entra ID via SAML/OIDC, ensuring the initial login is protected by your Conditional Access MFA rules.
- Review Authentication Methods: Ensure users are registered for secure MFA methods (like the Microsoft Authenticator app) rather than relying solely on vulnerable SMS.
Phase 3: Documentation Integration (Weeks 2-3)
- Download the SACS-210 Compliance Kit.
- Customize IAM Policies: Use the “Find and Replace” tool to instantly brand the Cybersecurity Policy and Acceptable Use Policy with your [Company Name].
- Complete Operational Forms: Integrate the Employee Onboarding and Offboarding Checklists into your HR workflows . Have all staff sign the AUP Acknowledgment Forms.
- Generate Audit Evidence: Export a list of all active users and their assigned roles from Entra ID. Paste this data into the Access Review Report template provided in the kit.
- Compile the Kit: Take clear screenshots of your Conditional Access policies and Password configuration screens, pasting them into the Final Technical Report.
Phase 4: Audit Preparation and Submission (Weeks 3-4)
- Conduct an Internal Pre-Audit Review: Use the Technical Implementation Checklist included in the Compliance Kit .
- Test Access Controls: Attempt logins from external networks to ensure Conditional Access successfully blocks or challenges the authentication.
- Engage an Authorized Audit Firm: Select an auditor from Saudi Aramco’s approved list.
- Submit Your Compliance Report: Hand over your perfect blend of Entra ID technical evidence and Kit-generated policy documentation.
Common Implementation Mistakes and How to Avoid Them
Even with Entra ID properly licensed, SMEs frequently misconfigure the environment. Avoid these common audit pitfalls:
- Blanket “Security Defaults” vs. Conditional Access: Turning on basic Security Defaults in Microsoft 365 is a great start, but it often lacks the granular reporting and specific enforcement targeting required by SACS-210 (TPC1.12). Solution: Upgrade to Entra ID Plan 1 and use explicitly defined Conditional Access policies.
- Failing to Document the Annual Access Review: SACS-210 mandates that you review user accounts and access rights at least annually (TPC1.14). Solution: Use the formal Access Review Report template from the Compliance Kit to document this process for the auditor.
- Incomplete Offboarding: Disabling the account in Entra ID but failing to document the hardware return and knowledge transfer violates TPC1.4. Solution: Strictly adhere to the written Employee Offboarding Checklist.
- Allowing Legacy Authentication: Legacy protocols bypass MFA. Solution:Create a Conditional Access policy that explicitly blocks legacy authentication clients.
Frequently Asked Questions
Q1: Can Microsoft Entra ID Plan 1 alone achieve SACS-210 compliance?
A: No. Entra ID handles the Identity and Access Management portion of the PROTECT domain. You still need solutions for endpoint protection, logging, and patch management. Furthermore, the technical controls require documented administrative policies. The SACS-210 Compliance Kit provides the missing paperwork framework.
Q2: Do I need to buy Entra ID Plan 1 standalone?
A: You can, but it is highly recommended to purchase Microsoft 365 Business Premium, which natively includes Entra ID Plan 1, along with Microsoft Intune (device management) and Defender for Business (endpoint protection). This covers almost all your technical bases in one license.
Q3: How do I procure Microsoft Entra ID licenses?
A: As an authorized Microsoft Cloud Solution Provider (CSP) based in Dammam, NHR Alemtithal offers direct procurement through our secure store.
Get Microsoft 365 Business Premium (Entra ID Included) Here
Q4: Can the SACS-210 Compliance Kit be used if we don’t use Microsoft?
A: Yes. The administrative policies, registers, and operational checklists in the Compliance Kit are platform-agnostic. However, the technical implementation steps are highly optimized for Microsoft environments.
Q5: How long does the entire implementation process take?
A: For a typical Saudi SME, the end-to-end process—from license procurement and Conditional Access configuration to CCC certificate submission—typically requires 3-4 weeks.
Q6: What ongoing maintenance is required after certification?
A: CCC certification is valid for two years. You must maintain your Microsoft subscriptions, conduct your documented annual access reviews , execute onboarding/offboarding checklists, complete yearly staff cybersecurity training, and prepare for a simplified re-audit.
Q7: Does this approach support NCA ECC 2:2024 and Saudi PDPL compliance?
A: Yes. The SACS-210 Compliance Kit is mapped to the NCA ECC 2:2024 and Saudi PDPL frameworks. Entra ID’s robust authentication and logging capabilities align perfectly with these national standards.
Accelerate Your CCC Certification Journey
Achieving SACS-210 compliance does not require spending heavily on fragmented, complex identity solutions. With Microsoft Entra ID Plan 1 acting as your identity perimeter, and the SACS-210 Compliance Kit serving as your administrative framework, Saudi SMEs can secure their Aramco CCC certification efficiently.
Your Next Steps
- Procure Licenses: Set up your technical foundation by purchasing Microsoft 365 Business Premium (which includes Entra ID Plan 1).
- Download the SACS-210 Compliance Kit: Access all 17 auditor-ready templates to bypass weeks of policy drafting.
- Configure Conditional Access: Implement MFA and access controls using the included technical checklist.
- Customize Your Evidence: Prepare your audit package using the customized Word and Excel documents.
- Engage an Auditor: Submit your perfectly aligned documentation and secure your contract.
Do not let weak access controls and missing paperwork delay your Aramco partnership.
Disclaimer: Microsoft Entra ID provides technical capabilities that support SACS-210 compliance. Proper configuration, ongoing management, and documented evidence are required to achieve certification. The SACS-210 Compliance Kit provides templates to support your efforts; template usage alone does not constitute certification. Organizations remain solely responsible for their cybersecurity posture and for validating compliance through an authorized third-party audit.