IT Managers in Saudi Arabia face the daunting task of translating corporate policy into technical reality. When preparing your infrastructure for the Saudi Aramco Cybersecurity Compliance Certificate (CCC), a critical question arises: what is access control in the eyes of an auditor? It is much more than just issuing passwords; it is the comprehensive, documented technical enforcement of who can access your systems, what they can do once inside, and how that access is continuously monitored. Drafting these policies from scratch and failing to map them to operational evidence can drain hundreds of hours from your department. Without proper documentation and technical logs, audit rejection is an imminent threat. This guide eliminates the guesswork, breaking down exactly how to align your Active Directory, MFA configurations, and employee lifecycle management with the SACS-210 (February 2026) General Requirements to ensure you are auditor-ready on day one.
5 Key Takeaways
- Centralized IAM is Mandatory: You must use Active Directory (or an equivalent IAM solution) to centralize user authorizations and enforce the principle of least privilege (TPC1.9).
- MFA is Non-Negotiable: Multi-factor authentication must be actively enforced for all remote access, cloud services, and privileged administrator accounts (TPC1.12).
- Stop Orphaned Accounts: Formal, documented IT sign-offs during employee onboarding and offboarding are required to prevent unauthorized access (TPC1.4).
- Audit Your Access: IT must conduct and document a formal review of all user accounts and access rights at least annually (TPC1.15).
- Restrict Local Admins: Standard users must be restricted from having local administrator rights on their workstations to prevent unauthorized software installations and policy modifications.
The Foundation: What Is Access Control in the CCC Context?
IT teams often rely on decentralized credentials, local workstation accounts, or shared administrative logins out of convenience. Auditors immediately flag these practices. Without a centralized directory, it is impossible to enforce Role-Based Access Control (RBAC) or adequately segregate duties.
Control Reference: TPC1.9 – Centralized IAM & Access Control.
Why auditors reject this: Shared generic accounts strip away individual accountability, making it impossible to determine who performed a specific action on the network. Furthermore, without centralized management, revoking access across all systems simultaneously is highly prone to human error.
The Fix: Implement a centralized Active Directory environment. Utilize the Procedure for Grant of Access Letter and the master Cybersecurity Policy from the SACS-210 Compliance Kit to formally govern how IT grants access. This establishes the paper trail the auditor needs to verify your technical configurations.

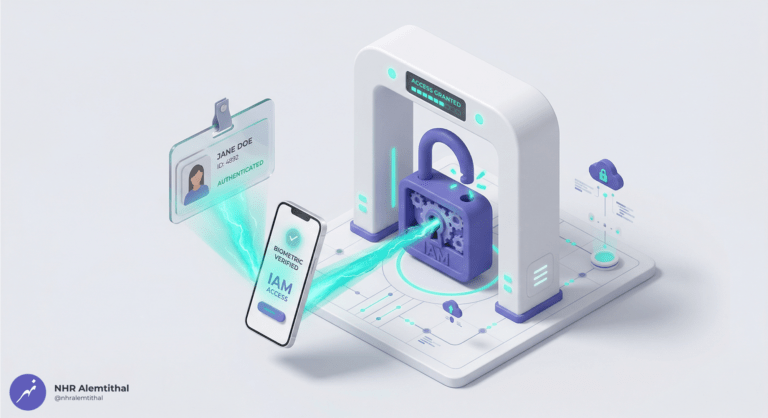
Enforcing Password and Authentication Management
Users frequently resist complex passwords, and legacy IT environments often lack native Multi-Factor Authentication (MFA). However, the standard is incredibly strict regarding how authentication must be handled.
Control Reference: TPC1.11 – Password and authentication management; TPC1.12 – Multi-factor authentication (MFA).
Why this matters: Passwords must be 8-64 characters in length and require alphanumeric complexity. More importantly, MFA is strictly required for all remote access (including VPNs and Remote Desktop), all cloud services (such as Microsoft 365 or Google Workspace), and all privileged accounts. Single sign-on (SSO) is permitted, but it must be coupled with MFA upon initial login.
The Fix: Force these configurations via Group Policy (GPO) and your IAM console. Use the kit’s Acceptable Use Policy (AUP) and the AUP Acknowledgment Form to legally bind users to these strict rules, giving IT the authority to enforce them without pushback.
The Employee Lifecycle: Onboarding and Offboarding
“Orphaned accounts” remain active long after an employee leaves the company, presenting a massive security vulnerability and an easy target for threat actors.
Control Reference: TPC1.4 – On-boarding and off-boarding process.
Why auditors reject this: Discovering an active account belonging to a former employee is an automatic major finding during a SACS-210 audit. It proves that IT and HR are disjointed and that the network is exposed.
The Fix: You must integrate the Employee Onboarding Checklist and Employee Offboarding Checklist templates into your HR and IT workflows. These forms provide explicit operational evidence that IT securely provisions unique credentials upon hire, and revokes network access, email, and VPNs immediately upon termination.

Continuous Auditing and Access Reviews
Access creep occurs naturally in any organization; employees change roles, departments, or projects, retaining old privileges while gaining new ones. Over time, standard users accumulate administrative rights.
Control Reference: TPC1.15 – Review user accounts/access annually.
Why auditors reject this: IT managers often perform routine cleanups of Active Directory but fail to formally document the process. Auditors require hard, documented proof that a comprehensive review took place.
The Fix: Deploy the Access Review Report template from the compliance suite. This document formalizes your review of Active Directory, ERP systems, and Cloud applications. It outlines the scope, lists anomalies found (such as excessive permissions), and acts as the exact artifact the auditor will request to satisfy TPC1.15.

Logging, Monitoring, and Protecting Evidence
If unauthorized access occurs, IT cannot trace the origin, scope, or impact without proper logging mechanisms. Access control is meaningless if you cannot monitor it.
Control Reference: TPC1.31 – Audit and cybersecurity event logs.
Why this matters: Your systems must be capable of logging critical events such as successful and failed logins, addition or deletion of user accounts, escalation of privileges, and modifications to security policies. These logs must be synced to a unified Network Time Protocol (NTP) source and protected from unauthorized deletion or tampering.
The Fix: Configure your edge firewalls, Windows servers, and critical applications to forward logs to a centralized, restricted syslog server or SIEM. Use the Technical Implementation Checklist provided in the kit to ensure your IT infrastructure is capturing the exact event attributes (Timestamp, User ID, Source IP, etc.) mandated by Appendix C of the standard.
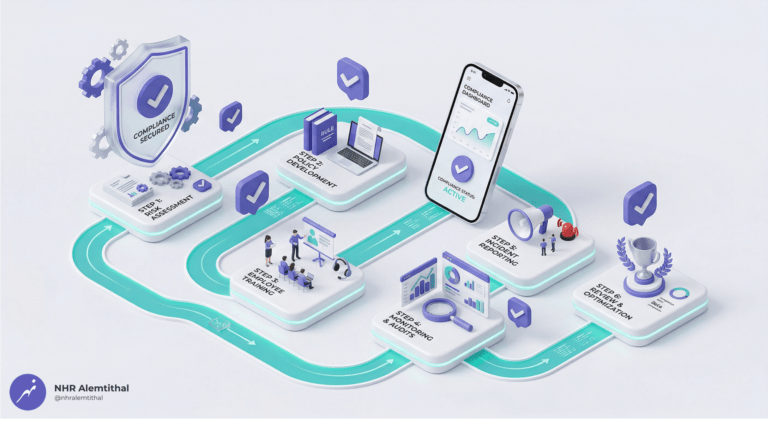
Access Control Prevention Checklist / Implementation Guide
To bridge the gap between policy and IT operations, ensure your technical team executes the following steps using the SACS-210 Compliance Kit templates:
- Deploy Centralized Directory: Ensure Active Directory (or equivalent) is fully operational to govern all workstation and server logins.
- Enforce GPOs: Configure Group Policy to mandate 8-64 character passwords, enforce screen lock timeouts (10-15 minutes), and block macro execution.
- Activate MFA universally: Turn on Multi-Factor Authentication for your Microsoft 365 tenant, all VPN portals, and IT administrator accounts.
- Operationalize HR Forms: Train HR to require IT sign-offs on the Employee Onboarding Checklist and Employee Offboarding Checklist for every personnel change.
- Conduct the Annual Audit: Download the Access Review Report template, review your active users against payroll, strip unnecessary permissions, and have the GM sign the final report.
Frequently Asked Questions
Q1: What is access control in the context of the SACS-210 General Requirements?
A: In SACS-210, access control (TPC1.9) is the technical and administrative enforcement of user identities, ensuring access is granted on a “Need-to-Know” basis using unique credentials and centralized management like Active Directory.
Q2: Does SACS-210 require MFA for standard office workers?
A: MFA is strictly mandated for all remote access (VPNs), cloud services (like company email), and privileged/administrative accounts (TPC1.12).
Q3: Can my IT department use shared administrator accounts to manage servers?
A: No. TPC1.10 demands that user authentication be granted based on unique credentials, and the technical guidelines explicitly state to disable or strictly control shared generic accounts.
Q4: How do we prove to the auditor that we manage employee terminations securely?
A: You must provide operational evidence. The Employee Offboarding Checklist from our kit, signed by IT with timestamps showing when network access was disabled, serves as the required artifact for TPC1.4.
Q5: We use single sign-on (SSO). Is that compliant?
A: Yes, TPC1.13 allows SSO, but it must be coupled with MFA upon the initial login to the system.
Q6: What specific logs do we need to retain for access control auditing?
A: According to Appendix C of the standard, you must log failed/successful login attempts, addition/deletion of user accounts, escalation of privileges, and the activities of privileged accounts.
Q7: Can we pass the audit by just showing our IT configurations?
A: No. Auditors require both technical configurations and approved governance documentation. You must have an approved Acceptable Use Policy and Cybersecurity Policy to back up your IT infrastructure.
Eliminate Guesswork and Get Auditor-Ready IT Templates
Stop wasting your department’s valuable technical hours drafting policies from scratch. Equip your IT team with the precise documentation an auditor wants to see.
| Feature | IT Manager Benefit |
| Technical Implementation Checklist | Translates confusing standard jargon into actionable IT configurations (GPOs, AD rules, MFA). |
| Pre-Mapped Forms & Reports | Ready-to-use templates like the Access Review Report (TPC1.15) to prove operational compliance instantly. |
| Instant Digital Download | Deploy 17 customizable .DOCX and .XLSX files across your network today. |
Secure your environment and fast-track your audit preparation.
Get the complete SACS-210 Compliance Kit (Feb 2026 Standard) via Instant Digital Download for a one-time cost of SAR 1,999 (VAT Included).