Editor’s Note: This guide has been fully updated to reflect the new Saudi Aramco SACS-210 Third-Party Cybersecurity Standard requirements released for February 2026.
The vendor landscape for Saudi Aramco is shifting rapidly, and for many businesses in the Eastern Province, the window to adapt is closing. If you operate a small to medium enterprise in Dammam, Khobar, or Jubail, competitive pricing and operational excellence are no longer enough to secure a contract. The new gatekeeper is cybersecurity.
According to the updated Third-Party Cybersecurity Standard (SACS-210, February 2026), ALL third parties engaging with Saudi Aramco through contractual agreements must obtain the Cybersecurity Compliance Certificate (CCC) before business can commence. This is not optional. This is not negotiable.
The problem? Most Saudi SMEs approach CCC certification like a paperwork exercise. They severely underestimate the technical complexity of the 33 General Requirements controls introduced in the February 2026 update. They try to write policies from scratch, misconfigure their systems, burn through budgets exceeding SAR 50,000 on IT consultants, and ultimately fail their first audit.
This guide changes that.
Aramco CCC Certification (SACS-210) Key Takeaways
- CCC certification is mandatory for ALL new Aramco vendors under the General Requirements classification.
- 33 cybersecurity controls (TPC1.1 to TPC1.33) must be fully implemented and evidenced under the new February 2026 standard.
- Certification validity must be maintained, and you must renew the CCC before it expires.
- Remote assessment is available for General Requirements (CCC), whereas CCC+ requires deeper scrutiny.
- Premium documentation kits exist to bypass SAR 15,000+ consulting fees, giving you an auditor-ready framework instantly.
- New 2026 requirements include enhanced data protection (TPC1.18), strict incident response SLAs (TPC1.32), and rigorous access management (TPC1.9).
What Is Aramco CCC Certification?
The Cybersecurity Compliance Certificate (CCC) is Saudi Aramco’s mandatory certification program that verifies third parties meet minimum cybersecurity requirements defined in the Third-Party Cybersecurity Standard .
The February 2026 update significantly expanded the baseline expectations for all vendors. The General Requirements now demand comprehensive controls , with a stronger emphasis on:
- Legislative and regulatory compliance: Continuous compliance with KSA laws and regulations (TPC1.1).
- Data protection and encryption: Aligned with KSA National Cryptographic Standards (NCS-1:2020) (TPC1.18).
- Incident response: Mandatory notification to the proponent within 24 hours of discovering an incident (TPC1.32).
- Employee lifecycle: Formal onboarding and offboarding procedures, including asset return (TPC1.4).
Asset inventory: Maintaining an accurate inventory of all technology assets (TPC1.8).
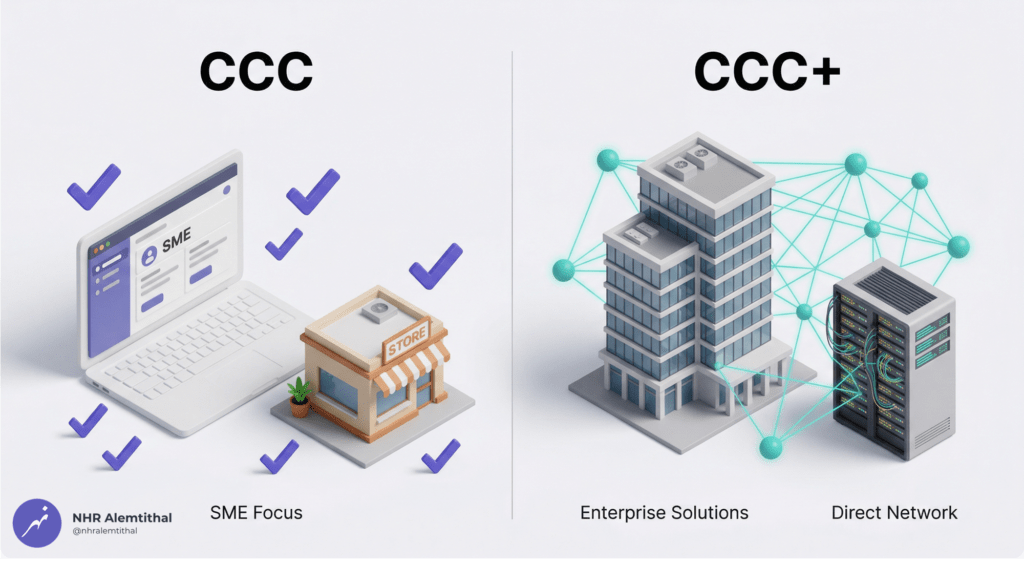
CCC vs. CCC+: Which Does Your SME Need?
| Certificate Type | Classification | Assessment Approach | Typical For |
| CCC | General Requirements | Remote self-compliance assessment verified by Authorized Audit Firm | Most Saudi SMEs |
| CCC+ | Network Connectivity, Outsourced Services, Critical Data Processor, Cloud Computing | On-site compliance assessment by Authorized Audit Firm | Large enterprises with direct network access or data hosting |
Good news for most SMEs: If you are a new vendor applying for general supply or service contracts in Dammam or Jubail, you likely fall under General Requirements—meaning standard CCC applies, not CCC+.
SACS-210 General Requirements: The 33 Controls You Must Pass
The General Requirements section (February 2026) contains 33 mandatory controls (TPC1.1 through TPC1.33) . Every single control must be implemented with supporting evidence. Here is the complete breakdown:
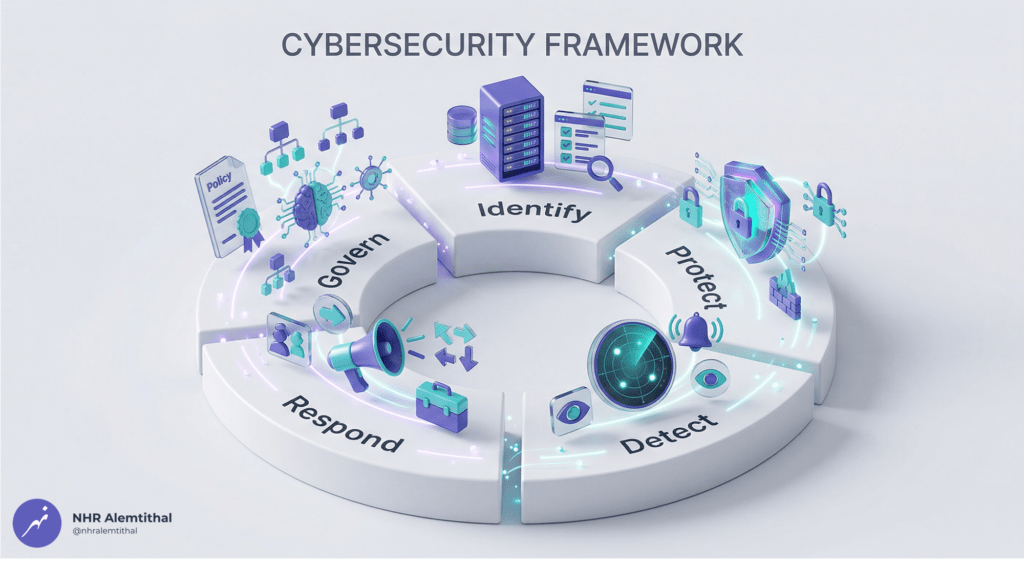
GOVERN Domain Controls
| Control | Requirement | Evidence Needed |
| TPC1.1 | Legislative and regulatory compliance (KSA cybersecurity laws) | Compliance register, self-assessment matrix |
| TPC1.2 | Acceptable Use Policy (AUP) | Approved policy document, employee acknowledgment forms |
| TPC1.3 | Cybersecurity Policies (asset management, access, physical security, sanitization, classification, incident, BCDR) | Comprehensive policy suite with all 8 required domains |
| TPC1.4 | Employee onboarding (background checks) and offboarding (asset return, access removal) | Onboarding and offboarding checklists, signed forms |
| TPC1.5 | Obtain CCC Certificate from authorized audit firm | Valid CCC certificate |
| TPC1.6 | CCC renewal before expiration | Renewal tracking, latest CCC copy |
| TPC1.7 | Proponent data shared only with contracted personnel | Data sharing policy, access logs |
IDENTIFY Domain Controls
| Control | Requirement | Evidence Needed |
| TPC1.8 | Maintain inventory of all information and technology assets | Asset inventory register (hardware, software, data) |
PROTECT Domain Controls
| Control | Requirement | Evidence Needed |
| TPC1.9 | User authorizations via centralized IAM (need-to-know, least privilege) | Access control policy, IAM system screenshots |
| TPC1.10 | Unique authentication credentials for all users | User account documentation |
| TPC1.11 | Password rules: 8-64 characters, lowercase, uppercase, digits, special characters, no hints | Password policy, Active Directory configuration screenshots |
| TPC1.12 | MFA enforced on: remote access, cloud services, company email, internet-facing applications, privileged accounts | MFA configuration evidence for all categories |
| TPC1.13 | Single sign-on (SSO) must use MFA on initial login | SSO and MFA configuration |
| TPC1.14 | Annual review of user accounts and access rights | Access review report (mandatory) |
| TPC1.15 | All Third-Party Technology Assets authenticated securely | Authentication logs, system configurations |
| TPC1.16 | Proponent data securely returned and deleted at end of data lifecycle | Data deletion certificates, return logs |
| TPC1.17 | Secure disposal of technology assets at end of lifecycle | Disposal certificates, sanitization records |
| TPC1.18 | Encrypt data at rest and in transit per KSA NCS-1:2020 advanced level | Encryption policy, technical implementation evidence |
| TPC1.19 | Restrict and secure external storage media usage | Removable media policy, DLP configurations |
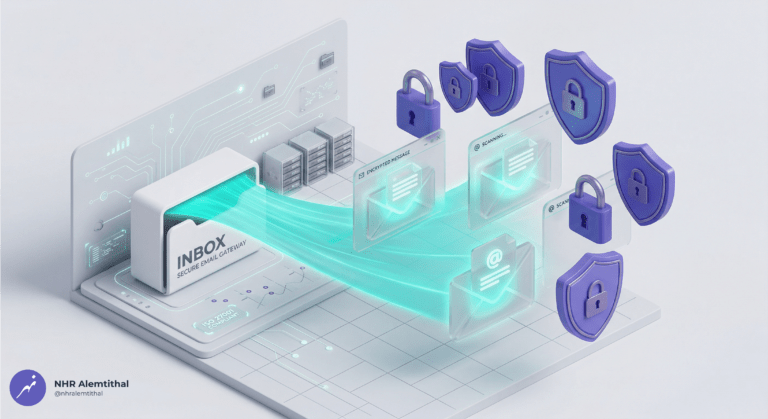
| TPC1.20 | Implement SPF, DMARC, and DKIM on mail server | DNS records, email security configurations |
| TPC1.21 | Inspect all incoming emails from Internet using anti-spam | Email security appliance evidence |
| TPC1.22 | Inspect all email attachments with signature analysis | Antivirus and anti-malware configurations |
| TPC1.23 | Use private email domain (Generic public domains like Gmail/Hotmail are prohibited) | Company domain registration, email configurations |
| TPC1.24 | Auto-block Microsoft Office Macros from external sources | Office 365 or G Suite macro settings |
| TPC1.25 | Synchronize all technology assets with authorized time source (NTP) | NTP configuration screenshots |
| TPC1.26 | Protect event logs from alteration, destruction, unauthorized access | Log protection policy, SIEM configurations |
| TPC1.27 | Firewalls enabled on all endpoint devices | Firewall settings on workstations and servers |
| TPC1.28 | Inspect all HTTP/HTTPS traffic from internet-facing apps using WAF | WAF configuration, traffic logs |
| TPC1.29 | Signature-based, up-to-date virus and malware protection | Antivirus installation, update logs, scan schedules |
| TPC1.30 | Test security patches before production; ensure recovery is possible | Patch management policy, test environment evidence |
DETECT Domain Controls
| Control | Requirement | Evidence Needed |
| TPC1.31 | Activate audit and cybersecurity event logs | SIEM logs, audit trail samples |
RESPOND Domain Controls
| Control | Requirement | Evidence Needed |
| TPC1.32 | Notify proponent within 24 hours of discovering cybersecurity incident | Incident response policy, notification logs, 24-hour SLA evidence |
| TPC1.33 | Notify proponent when employees with credentials no longer need access | Access revocation logs, notification emails |
Common Mistakes That Cause Audit Failure (2026 Update)
Based on audit patterns observed across Saudi SMEs, here are the 7 critical mistakes that result in CCC certification delays:
- Using Generic Email Domains: Gmail, Hotmail, or Yahoo addresses for business communications explicitly violate TPC1.23. Solution: Register and configure a private company domain.
- Missing MFA on Cloud Services: Microsoft 365 or other cloud services without Multi-Factor Authentication fail TPC1.12. Solution: Enable MFA on ALL remote access and cloud service accounts before audit submission.
- Incomplete Password Policy Evidence: Your written policy exists, but the technical configuration does not match the strict 8-64 character limit with symbols required by TPC1.11. Solution: Provide BOTH the policy document AND Active Directory/Local security screenshots.
- No Training Attendance Records: Security training was conducted, but you have no documentation proving employee participation. Solution: Maintain signed attendance sheets.
- Unpatched Systems at Audit Time: Operating system or software patches are not current during evidence collection, violating TPC1.30. Solution: Run Windows Update and document patch status before the audit.
- Anti-Virus Not Configured Properly: Antivirus is installed, but scans are not scheduled or signature updates are not daily, violating TPC1.29. Solution: Configure automatic daily updates and full scans with logs.
- Selecting Wrong Audit Firm: Contracting an audit firm not on Saudi Aramco’s Authorized list violates TPC1.5. Solution: Verify auditor authorization before signing any contracts.
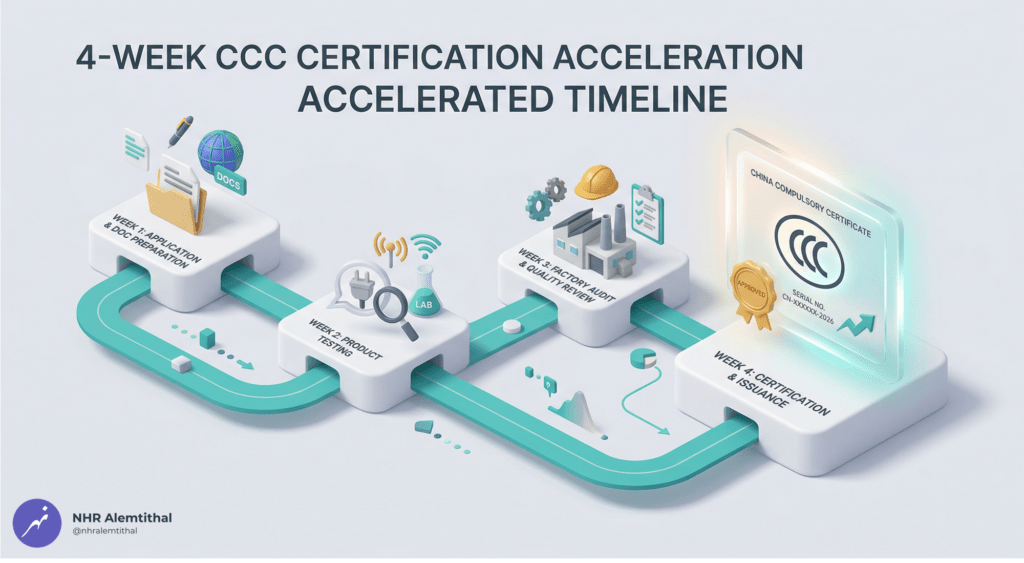
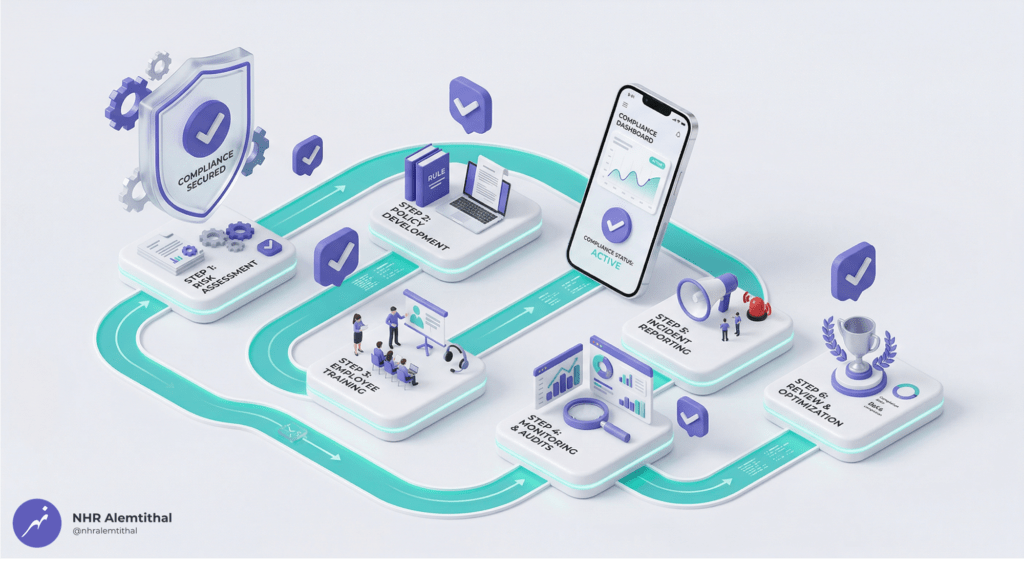
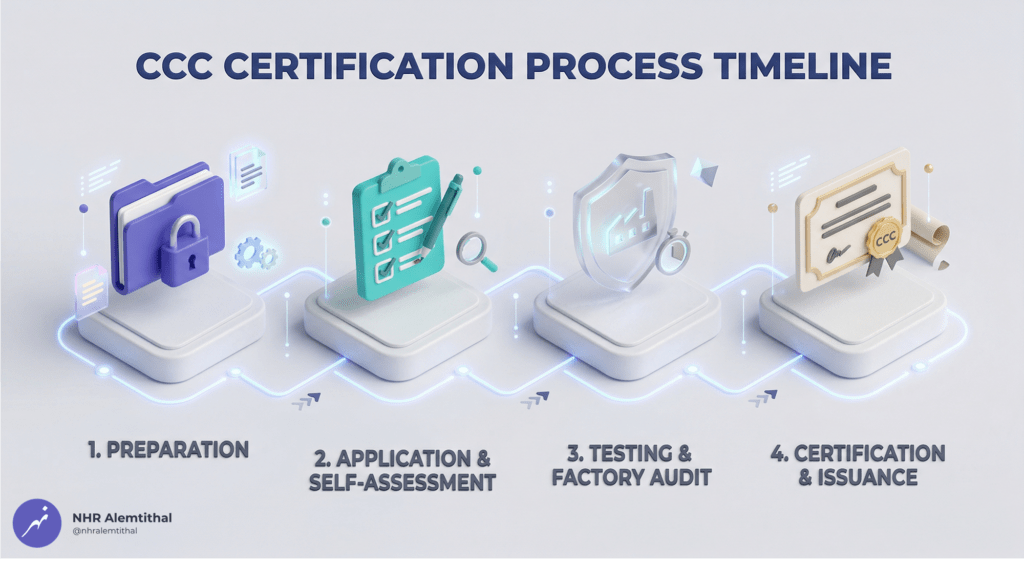
Step-by-Step Aramco CCC Certification Process (2026)
Following the latest standards, here is the official certification pathway:
Phase 1: Preparation (Week 1)
- Confirm your company classification (General Requirements = CCC) .
- Complete the Third-Party Classification Template and Confirmation Letter.
- Implement all 33 General Requirements controls (TPC1.1 through TPC1.33) .
- Deploy technical controls (MFA, firewalls, antivirus, email security, encryption).
(Pro Tip: Use a compliance documentation kit to instantly access all required policies, forms, and registers pre-mapped to each control.)
Phase 2: Self-Assessment (Week 2)
- Fill out the Third-Party Cybersecurity Compliance Report.
- Gather all evidence (screenshots, policies, logs, registers).
- Ensure evidence is clear, readable, and timestamped.
- Complete the mandatory Access Review Report (TPC1.14) and Asset Inventory Register (TPC1.8).
Phase 3: Audit Firm Engagement (Weeks 2-3)
- Select an Authorized Audit Firm from Aramco’s approved list.
- Establish a contract and submit your Compliance Report plus Classification documents.
- The audit firm verifies your documents remotely. Address any findings or gaps identified.
Phase 4: Certification and Submission (Weeks 3-4)
- The audit firm issues the CCC Certificate (if 100 percent compliant).
- Submit the CCC plus Compliance Report to the Saudi Aramco e-Marketplace.
- Maintain your documentation and set a renewal reminder before expiration (TPC1.6).
What Is Inside the SACS-210 Compliance Kit?
Building these 33 policies, tracking registers, and forms from scratch is a time-consuming, complex process that risks audit failure if done incorrectly .
The SACS-210 Compliance Kit (Feb 2026 Standard) – Complete Documentation Suite is a premium, fully customizable digital toolkit designed to save you weeks of drafting and guarantee audit readiness .
Here is exactly what is included in the digital download:
01 Policies (The Foundation)
- Cybersecurity Policy: The master governance document mapped to SACS-210 and NCA ECC 2:2024.
- Acceptable Use Policy (AUP): Defines remote work, AI usage, and password rules.
02 Forms (Operational Evidence)
- AUP Acknowledgment Form
- Employee Onboarding Checklist Form
- Employee Offboarding Checklist Form
- Policy Exception Request Form
- Third-Party Classification Confirmation Letter
- Inapplicable Controls Form Template
03 Registers (Dynamic Excel Trackers)
- Asset Inventory Register: Tracks hardware, software, and data repositories.
- Legislative & Regulatory Register: A live compliance tracker and quarterly self-assessment matrix.
04 Reports (Audit Deliverables)
- Access Review Report.
- Interim Status Report.
- Final Technical Report & Final Business Report
05 Official Letters and Memos
- Confirmation and Commitment for Current Environmental Status
- Ownership Confirmation Memo
- Remote Access Inapplicability Letter
- Procedure for Grant of Access to Aramco Vendor Portal
Bonus: The SACS-210 User Guide
- Step-by-step customization guide for each document.
- Technical Implementation Checklist for your IT team (MFA, firewalls, backups, log protection).
Format: DOCX (Microsoft Word) and XLSX (Microsoft Excel) in a compressed ZIP.
Delivery: Instant Digital Download.
Frequently Asked Questions
Q1: How long does CCC certification take for new vendors?
A: Typically 2-4 weeks from starting the process to certificate delivery, depending on your implementation speed. Utilizing the SACS-210 Compliance Kit cuts your documentation preparation time from weeks to just a few hours.
Q2: Can we complete certification without an internal IT team?
A: Yes. The documentation kit model is designed specifically for SMEs without dedicated IT staff. The kit includes a plain-English Technical Implementation Checklist you can hand to any outsourced IT provider or MSP to configure your firewalls and MFA.
Q3: What happens if we fail the audit?
A: If you implement all recommended controls properly using an auditor-aligned documentation suite, your chances of failure drop near zero. If an auditor spots a gap (e.g., a missing screenshot), they issue a finding. You simply correct the technical gap, update your evidence, and resubmit.
Q4: How much does it cost to get CCC certified?
A: Traditional IT consultants in the Eastern Province often charge SAR 15,000 to SAR 25,000 just to draft your security policies from scratch, not including the actual auditor fees. By utilizing a premium, pre-built documentation toolkit, you bypass these massive consulting fees entirely, allowing you to allocate your budget solely to the necessary software tools (like Microsoft 365) and the Authorized Audit Firm.
Q5: Do we need on-site auditor visits for General Requirements?
A: No. General Requirements classification uses remote assessment. Only CCC+ classifications (Network Connectivity, Critical Data Processor) require on-site visits.
Q6: How do we maintain CCC certification after 2 years?
A: Renewal involves a simplified re-audit. You must update your policies, verify continued compliance with the 33 controls, conduct your annual access reviews (TPC1.14) , maintain your asset inventory (TPC1.8), and complete yearly cybersecurity training for all staff.
Q7: What if we do not have remote access or cloud services?
A: You can submit a Remote Access Inapplicability Letter (included in the SACS-210 Compliance Kit) to formally document to the auditor why certain controls do not apply to your environment.
Ready to Secure Your Aramco Partnership?
Your Aramco contract is waiting. The only question is: Will CCC certification delay it?
The February 2026 standard is more comprehensive than ever. Trying to build 33 controls’ worth of policies and registers from scratch guarantees weeks of drafting, missing critical evidence, and risking audit failure.
The SACS-210 Compliance Kit (Feb 2026 Standard) – Complete Documentation Suite provides the exact administrative foundation you need.
Your Next Steps
- Download the SACS-210 Compliance Kit to get instant access to all 17 templates.
- Customize the documents: Use “Find and Replace” for Company Name placeholders.
- Implement technical controls: Follow the included Technical Implementation Checklist.
- Engage an authorized audit firm and submit your evidence.
Do not let missing paperwork become your contract bottleneck.
Disclaimer: The SACS-210 Compliance Kit provides templates and guidance to support compliance efforts. Template usage alone does not constitute certification. Full compliance requires technical implementation of security controls (e.g., configuring firewalls, enabling MFA), staff training, evidence generation over operational periods, and validation through an authorized third-party audit. Organizations remain solely responsible for their cybersecurity posture.