In our last post, we introduced DMARC as your brand’s unseen guardian. But DMARC doesn’t work in isolation. It’s the leader of a powerful trio of technologies that, together, form the foundation of modern email security.
Understanding how these three “musketeers”—SPF, DKIM, and DMARC—collaborate is key to seeing why you need all of them to protect your business from email fraud.
Let’s use a simple analogy: sending a secure package.
SPF: The Return Address (Who is allowed to send this?)
SPF stands for Sender Policy Framework.
Think of SPF as the official return address stamped on the outside of your package. It’s a public list you create that tells the world, “Only packages sent from these specific post offices are legitimately from me.”
In technical terms, SPF is a DNS record where you list all the IP addresses of the servers authorized to send email for your domain (e.g., Microsoft 365’s servers, your marketing email provider’s servers, etc.).
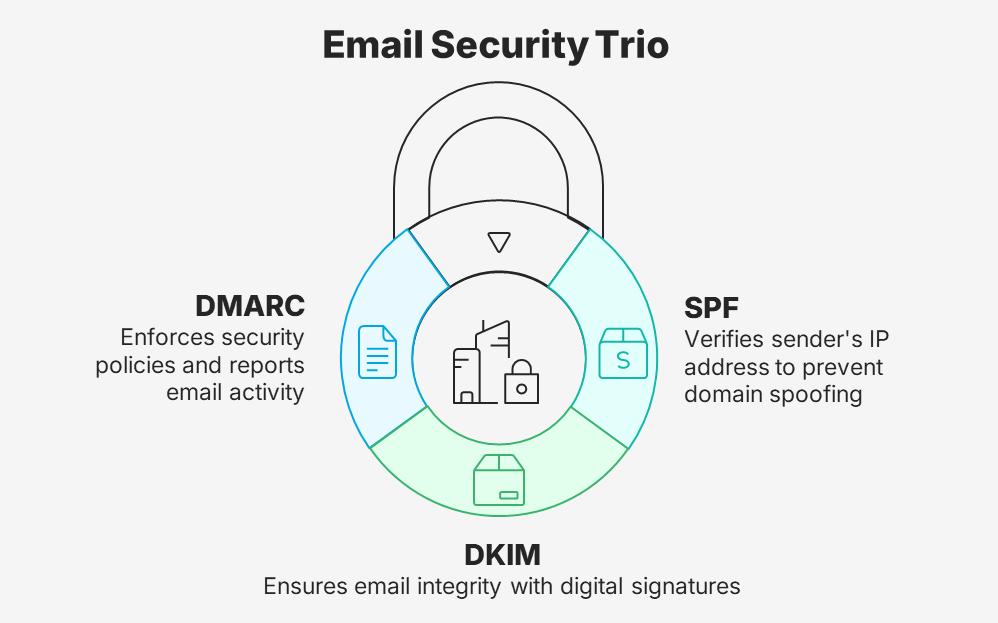
- What it does: It helps prevent simple domain spoofing by checking if the sending server is on your approved list.
- Its weakness: If an email is forwarded, the “return address” can sometimes get smudged or misread, causing the check to fail even for legitimate mail.
DKIM: The Tamper-Proof Seal (Is this package authentic?)
DKIM stands for DomainKeys Identified Mail.
Now, imagine your package is sealed with a special, tamper-proof wax seal that is unique to your company. If anyone tries to open the package and change the contents, the seal will be broken.
DKIM works just like this. It adds a unique, encrypted digital signature to the header of every email you send. Receiving email servers can check this signature to verify two things:
- The email truly came from your domain.
- The content of the email has not been altered in transit.
- What it does: It proves the email’s integrity and authenticity.
- Its weakness: While it proves an email is authentic, it doesn’t tell the receiving server what to do if the seal is broken or missing. It just notes the problem.
DMARC: The Recipient’s Instructions (What should I do with this package?)
DMARC stands for Domain-based Message Authentication, Reporting, and Conformance.
DMARC is the set of instructions you give to the recipient of your package. It says: “When you receive a package from me, please check both the return address (SPF) and the tamper-proof seal (DKIM). If either one looks suspicious, here is exactly what I want you to do with it.”
DMARC unifies SPF and DKIM into a single, coherent policy. You can set one of three policies:
- p=none: “Just monitor and let me know about suspicious packages, but deliver everything.” (This is for gathering reports).
- p=quarantine: “Send suspicious packages to the spam folder.”
- p=reject: “Refuse to accept any suspicious packages at all.”
- What it does: It enforces your security policy, tells servers how to handle fraudulent email, and sends you reports on all email activity (legitimate and fraudulent) from your domain.
All for One, and One for All!
You need all three because they cover each other’s weaknesses:
- Without SPF and DKIM, DMARC has nothing to check.
- Without DMARC, SPF and DKIM are just informational—they don’t tell email servers to actually block fraudulent messages.
Implementing this security trio is the single most effective thing you can do to stop email impersonation, protect your brand, and ensure your emails reach their destination.
Ready to put the three musketeers to work for your business? Our Domain Shield service is a one-time setup that configures all three protocols correctly, giving you comprehensive protection without the complexity.